Blue-Green Deployment for Carrier Integration: Zero-Downtime API Migration Patterns That Preserve Multi-Tenant Isolation During the 2026 Transition Wave

USPS Web Tools API platform was retired on January 25, 2026, and FedEx SOAP web services must migrate by March 31, 2026. These aren't isolated changes. API downtime increased by 60% in Q1 2025 compared to Q1 2024, with average uptime dropping from 99.66% to 99.46%. For carrier integration platforms processing millions of labels daily, this perfect storm demands deployment strategies that won't add to the reliability crisis.
Standard blue-green deployment guides assume your application is a simple web service with shared-nothing architecture. Carrier integration middleware breaks those assumptions in ways that make deployment failures expensive and recovery complex.
The 2026 Carrier API Migration Challenge
The USPS Web Tools API platform officially shuts down on Sunday, January 25, 2026. After this date, all Web Tools integrations will stop functioning. The new USPS API Platform is a modern, OAuth 2.0–based system that replaces legacy Web Tools APIs, introducing new endpoints, authentication methods, and versioned services.
FedEx follows a similar pattern. FedEx Web Services tracking, Address Validation, and Validate Postal Codes Web Services were retired on May 15, 2024, with SOAP-based FedEx Web Services in development containment, replaced with FedEx RESTFUL APIs. The changeover to OAuth authorization must be completed by March 31, 2026.
These aren't optional upgrades. Integration platforms like EasyPost, Cargoson, nShift, and ShipEngine face simultaneous migrations across their entire carrier portfolio while maintaining service for existing customers.
Why Standard Blue-Green Falls Short for Carrier Integration
Blue-green deployment allows you to upgrade production software without downtime by deploying the new version into a copy of the production environment and changing routing to switch. This works beautifully for stateless applications. Carrier integration middleware presents three problems that break standard patterns:
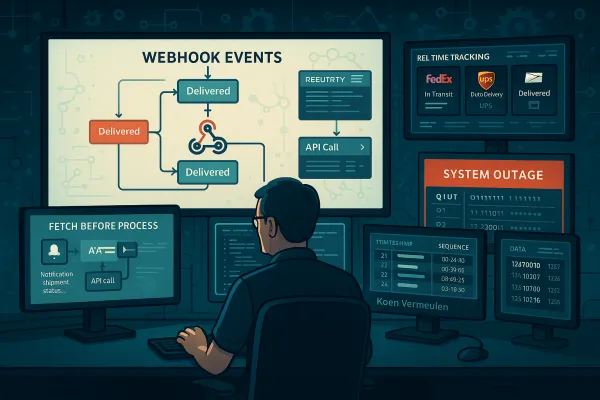
Webhook Endpoint Consistency: Carriers deliver status updates to registered webhook URLs. When you switch traffic from blue to green, existing shipments continue sending callbacks to the old environment unless you coordinate endpoint migration with each carrier.
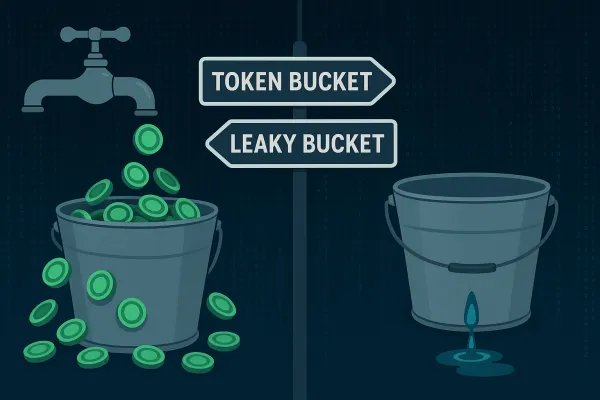
Rate Limiting Coordination: Carriers enforce rate limits per API key or account. Running parallel blue and green environments can trigger rate limit violations if both environments authenticate with the same credentials during testing.
Tenant Data Isolation: Multi-tenant platforms can't risk cross-tenant data exposure during cutover. Each tenant may use different carrier accounts, authentication credentials, and webhook configurations that must remain isolated throughout the deployment.
Traditional blue-green assumes you can test the green environment against the same external dependencies as blue. Carrier APIs don't work this way. Sandbox environments rarely match production behavior, and production testing with real shipments creates actual packages, billing, and customer impact.
Multi-Tenant Blue-Green Architecture Pattern
The solution extends blue-green deployment with tenant-aware traffic routing and coordinated resource management. Here's the architecture that handles carrier integration constraints:
Tenant-Aware Traffic Routing
Instead of switching all traffic at once, route based on tenant context. Your load balancer configuration should support these routing patterns:
Percentage-Based Tenant Migration: Start with low-risk tenants or a small percentage of your tenant base. Route specific tenant IDs to the green environment while others remain on blue.
Carrier-Specific Rollout: If migrating carrier APIs, route tenants by which carrier integration they're using. Deploy USPS API changes to green while FedEx remains on blue.
Webhook URL Preservation: Maintain webhook endpoints in both environments during transition. Use a webhook proxy that can route callbacks to the correct environment based on shipment metadata.
Stateful Resource Management
Carrier integrations maintain state that crosses environment boundaries:
Authentication Token Coordination: Use separate carrier API credentials for blue and green environments where possible. For carriers that don't support multiple credential sets, implement token sharing with proper synchronization.
Rate Limit State Sharing: Deploy a shared rate limiting service that coordinates between blue and green. This prevents the combined load from both environments triggering carrier API limits.
Database Connection Strategy: Use separate database schemas or connection pools for blue and green, but share read-only reference data like carrier service codes and postal zone mappings.
Webhook Delivery Continuity Patterns
Webhook delivery failures during deployment create the worst user experiences. Customers see shipments stuck in "Label Created" status because status updates get lost during environment switching.
Dual Endpoint Registration: Register webhook endpoints in both blue and green environments with carriers that support multiple URLs. Route incoming webhooks to the environment that created the shipment.
Event Replay Mechanism: Implement a webhook replay system that can re-request status updates for shipments created near the cutover time. This catches callbacks that might have been delivered to the wrong environment.
Idempotency Key Preservation: Ensure webhook processing remains idempotent across environments. The same tracking update delivered to both blue and green should not create duplicate database entries or customer notifications.
The key insight: webhook continuity requires coordination with external systems (carriers) that don't participate in your deployment process. Build bridges, not hard cutovers.
Production Implementation Strategy
Pre-Migration Validation
Carrier sandbox testing reveals integration issues but rarely catches production-specific problems. Your validation strategy should include:
Contract Testing in Green: Deploy API client code that validates request/response schemas against carrier specifications without creating real shipments. This catches breaking changes in request formats.
Rate Limit Verification: Test authentication and basic carrier connectivity in green without generating significant API load. Verify OAuth token refresh works and error handling behaves correctly.
Webhook Endpoint Validation: Register test webhook endpoints and verify they're reachable from carrier networks. Many webhook failures occur due to firewall or DNS propagation issues.
Gradual Tenant Rollout
Start with internal test tenants, then low-volume customers, then high-volume shippers:
Tenant Selection Criteria: Choose initial tenants based on carrier usage patterns, label volume, and business impact. Avoid tenants with complex shipping rules or high SLA requirements for the first wave.
Per-Tenant Monitoring: Track error rates, API response times, and webhook delivery success separately for each tenant. This isolates failures and prevents cascade effects.
Automated Rollback Triggers: Define specific thresholds that trigger automatic rollback to blue: carrier API error rates above 5%, webhook delivery failures above 2%, or any authentication errors.
Monitoring and Observability During Migration
Standard application metrics miss carrier-specific failure modes. Your observability stack needs these additional signals:
Carrier-Specific SLIs: Monitor API success rates, response times, and error types separately for each carrier. A USPS API failure shouldn't mask a FedEx success rate improvement.
Webhook Delivery Metrics: Track webhook callback latency, duplicate detection rates, and replay queue depths. These indicate whether status update flow remains healthy during cutover.
Tenant Isolation Validation: Alert on any cross-tenant data access during deployment. This includes database queries returning data for unexpected tenant IDs or API calls using wrong authentication credentials.
Example Prometheus queries for carrier integration monitoring:
carrier_api_success_rate_5m = sum(rate(carrier_api_success_total[5m])) by (carrier, environment) / sum(rate(carrier_api_requests_total[5m])) by (carrier, environment)
webhook_delivery_lag_p95 = histogram_quantile(0.95, rate(webhook_delivery_duration_seconds_bucket[5m])) by (carrier, environment)
Common Pitfalls and Recovery Patterns
Real deployment failures in carrier integration follow predictable patterns:
Webhook Endpoint DNS Propagation: New green environment webhook URLs may not resolve from carrier networks immediately after DNS updates. Always verify webhook reachability from external networks before cutover.
Rate Limit State Divergence: Blue and green environments consuming from shared rate limit quotas can trigger unexpected throttling. Implement rate limit coordination or use separate carrier credentials where possible.
Authentication Token Expiry: OAuth tokens that work in blue may expire during green environment deployment. Implement proactive token refresh in both environments during migration windows.
Cross-Environment Shipment References: Tracking numbers or shipment IDs created in blue must remain queryable after cutover to green. Use shared read replicas or database views to maintain continuity.
These failures follow the same pattern: external dependencies (carriers) don't understand your deployment boundaries. Success requires building systems that work across environment transitions, not systems that assume clean cutovers.
Recovery from carrier integration deployment failures differs from typical application rollbacks. You can't simply switch traffic back to blue if green has already created shipments or registered new webhook endpoints with carriers. Build recovery procedures that coordinate with carrier state, not just your application state.
The 2026 carrier API migration wave creates unique pressure on integration platforms. Average weekly API downtime rose from 34 minutes in Q1 2024 to 55 minutes in Q1 2025, and traditional deployment strategies often contribute to this unreliability. Multi-tenant blue-green deployment patterns, designed specifically for carrier integration constraints, provide a path to zero-downtime API migrations that maintain the reliability your customers expect.