Multi-Tenant Hybrid EDI-API Gateway Architecture: Preserving Tenant Isolation While Supporting Real-Time Carrier Connectivity and Compliance Workflows
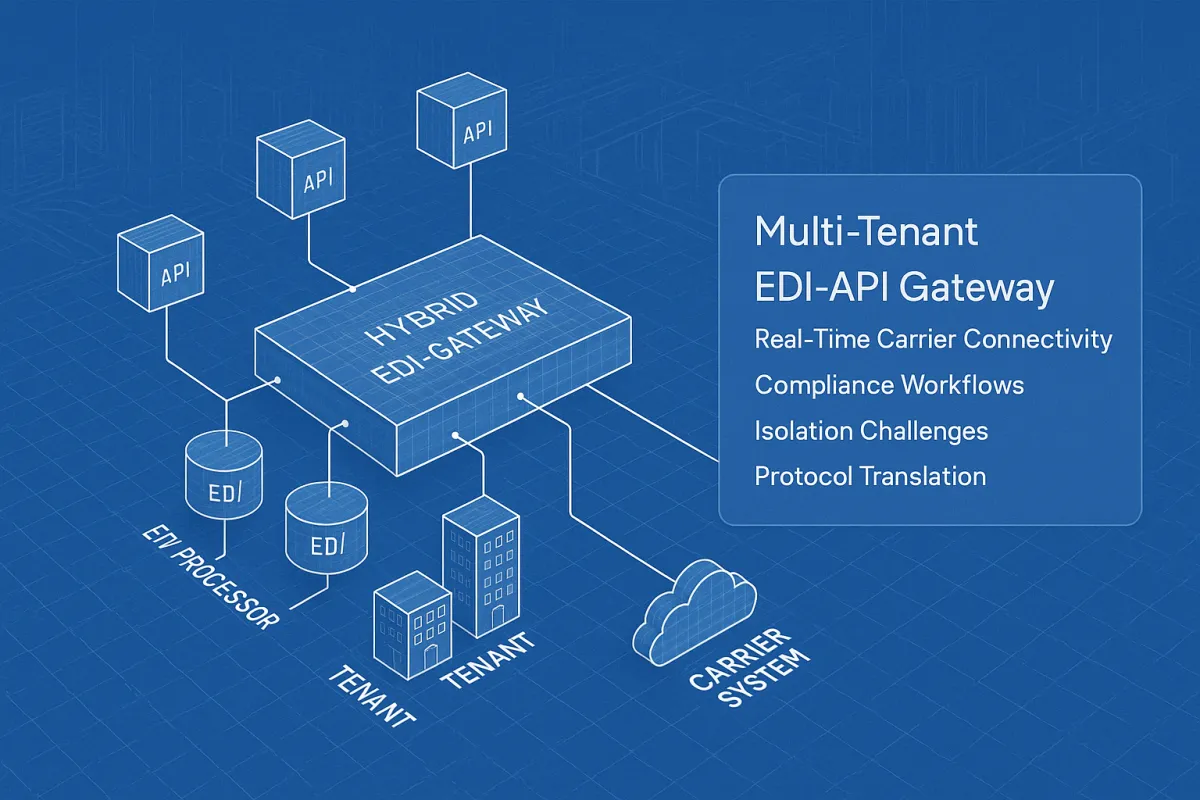
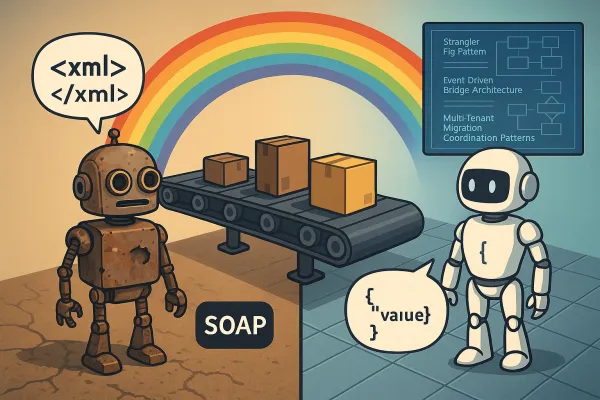
A hybrid approach is emerging where APIs handle real-time status updates while EDI manages complex, high-volume document exchanges. This pattern isn't just theoretical – leading 3PLs are using EDI-to-API gateways to translate old-school messages into modern JSON payloads, giving their developers a clean, unified environment to work in without breaking legacy connections.
The multi-tenant hybrid EDI-API gateway architecture represents the evolution of carrier integration platforms in 2026. Rather than forcing a binary choice between traditional EDI systems and modern APIs, the 2026 trend is an "API-First" approach, serving as a low-friction gateway for partners while EDI handles the heavy lifting behind the scenes. This architectural pattern addresses the reality that EDI remains the compliance backbone for retail trading partners, while APIs power real-time operational workflows.
Multi-Tenant Isolation Challenges in Hybrid Systems
Protocol translation in a multi-tenant environment creates unique isolation challenges that don't exist in single-protocol systems. Isolation refers to the controls that prevent one tenant's data or workloads from affecting another's. When your gateway translates between API calls and EDI documents, you're handling two data models simultaneously – the JSON payloads from APIs and the structured X12 or EDIFACT documents from EDI.
The "noisy neighbor problem," has become the hallmark performance issue of 2026. In hybrid gateways, this manifests when one tenant's bulk EDI file processing saturates translation resources, causing API response times for other tenants to degrade. One tenant's misconfiguration or resource spike can crash your entire cluster, requiring aggressive resource quotas and API rate limiting.
Consider tenant A submitting a 50MB EDI 856 advance ship notice file while tenant B expects sub-second API responses for rate shopping. Without proper isolation, the EDI parsing workload can consume CPU and memory resources, causing API timeouts. The problem is compounded by the fact that usage-based pricing makes isolation a hard business problem, not just a technical one. If you charge customers per API call, per data point processed, or per feature usage, you need isolation. Otherwise, a resource spike from customer A will increase the usage reported by customer B.
Modern isolation patterns use namespace-per-tenant in Kubernetes, VPC-per-tenant for network isolation, and hybrid models that combine shared infrastructure for standard customers with dedicated deployments for enterprise accounts. For hybrid gateways, this translates to separate processing queues for EDI and API workloads, tenant-scoped connection pools, and protocol-aware rate limiting.
Gateway Design Patterns for Protocol Translation
API gateways (e.g., Kong, Apigee) to translate modern API calls into legacy protocols (e.g., SOAP, EDI). The hub-and-spoke topology has become the dominant pattern, where a central integration hub routes and transforms data between endpoints. Useful for monolithic or legacy systems, but lacks agility.
Here's what a tenant-aware routing layer looks like in practice:
┌─────────────┐ ┌─────────────────┐ ┌─────────────────┐
│ Tenant A │───▶│ API Gateway │───▶│ EDI Processor │
│ (API) │ │ (Kong/Envoy) │ │ (X12/EDIFACT) │
└─────────────┘ │ │ └─────────────────┘
│ │ │
┌─────────────┐ │ Route/Transform│ ▼
│ Tenant B │───▶│ Per Protocol │ ┌─────────────────┐
│ (EDI) │ │ │ │ Carrier Systems │
└─────────────┘ └─────────────────┘ │ (AS2/SFTP/API) │
└─────────────────┘
The translation engine must handle envelope vs payload patterns efficiently. API requests typically carry business logic in JSON payloads, while EDI documents embed routing and compliance metadata in the envelope structure. Your gateway needs tenant-aware transformation rules that preserve this context during protocol conversion.
Platforms like Cargoson, nShift, EasyPost, and ShipEngine each implement different approaches to this hub-spoke model. Some prioritise synchronous API-to-EDI translation for real-time responses, while others use asynchronous queues to handle EDI's batch-oriented nature without blocking API clients.
Compliance and Audit Trail Considerations
Multi-tenant compliance becomes exponentially complex when you're managing audit trails across both EDI and API protocols. In a Zero-Trust model, every transaction is verified at every connection point so data is managed in compliance with relevant frameworks and regulations. Your audit logs must correlate API requests with their corresponding EDI transactions, maintaining tenant boundaries throughout the transformation process.
GDPR compliance requires particular attention in hybrid systems. An API delete request must propagate to any EDI documents generated from that data, and your retention policies must account for both protocol formats. Event sourcing patterns work well here – instead of deleting data, you append deletion events that apply to both API and EDI representations of the same business transaction.
Consider implementing immutable audit logs with tenant-scoped access controls:
{
"tenant_id": "acme_corp",
"correlation_id": "api_req_12345",
"event_type": "protocol_translation",
"api_request": {
"endpoint": "/v1/shipments",
"method": "POST",
"timestamp": "2026-03-18T14:30:00Z"
},
"edi_output": {
"transaction_set": "214",
"control_number": "000012345",
"timestamp": "2026-03-18T14:30:05Z"
},
"compliance_markers": ["GDPR", "SOC2", "HIPAA"]
}
This correlation enables end-to-end auditability while maintaining tenant isolation and supporting compliance reporting requirements across both protocols.
Performance and Scalability Patterns
The competitive advantage comes from synchronizing both through a unified integration layer that eliminates batch delays and data inconsistencies. However, performance optimisation in hybrid gateways requires understanding the fundamental differences between API and EDI processing patterns.
APIs excel at low-latency, high-frequency transactions. EDI thrives on high-throughput batch processing. Your gateway must optimise for both patterns simultaneously without letting one compromise the other. Traffic shaping algorithms become critical – you might allocate 70% of processing capacity to real-time API translations during business hours, then shift to 80% EDI batch processing during overnight windows.
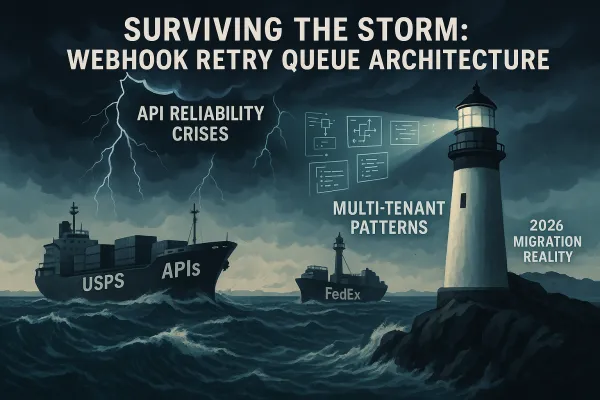
Carrier-specific rate limiting adds another complexity layer. FedEx APIs might allow 1,000 calls per minute, while their EDI AS2 connection accepts files every 15 minutes. Your tenant routing must respect these constraints while maintaining fair resource allocation across customers.
Memory management patterns differ significantly between protocols. API JSON parsing is typically streaming-friendly and memory-efficient. EDI X12 files often require loading entire transaction sets into memory for validation and transformation. Runtime isolation via Kubernetes resource quotas, connection pooling, and hardened container runtimes prevents application-level resource contention.
Consider implementing protocol-aware auto-scaling:
- API Pods: Scale based on request latency and queue depth (target: sub-200ms response times)
- EDI Pods: Scale based on file queue size and processing time (target: complete 1MB files within 30 seconds)
- Shared Resources: Connection pools to carrier systems, tenant authentication caches
Observability and Monitoring Across Protocols
APM strategies now emphasize business transaction correlation rather than isolated infrastructure metrics. Cloud-native monitoring, AI-driven instrumentation, and dependency mapping help SaaS teams understand how tenant workloads affect shared systems. Key metrics include onboarding time, integration uptime, API latency, connector error rates, and thresholds for noisy neighbor risk.
Your monitoring strategy must track the complete journey from API request to EDI delivery, correlating performance metrics across protocol boundaries. Traditional monitoring tools struggle with this hybrid approach – they're optimised for either API observability or batch job monitoring, not both.
Distributed tracing becomes essential for debugging cross-protocol issues. When a carrier rejects an EDI 997 functional acknowledgement that originated from an API shipment request, your traces must connect the rejection back to the original API call with full tenant context preserved.
Essential metrics for hybrid gateway observability:
- Protocol Translation Latency: API-to-EDI conversion time per tenant
- Cross-Protocol Success Rates: End-to-end delivery confirmation across both APIs and EDI
- Tenant Resource Utilisation: CPU/memory/network usage per tenant per protocol
- Compliance Violations: Failed validation rules, retry attempts, dead letter queue accumulation
- Carrier Integration Health: Response times and error rates for each carrier's API and EDI endpoints
Tools like Datadog, New Relic, and open-source alternatives like Grafana can aggregate these metrics, but you'll need custom instrumentation to capture the protocol translation layer effectively.
Implementation Roadmap and Migration Strategies
Organizations modernizing legacy environments often begin by decoupling translation from operational systems. If you are evaluating that shift, this resource on how to modernize legacy EDI systems outlines the transition path. The migration to a multi-tenant hybrid gateway requires careful orchestration to avoid service disruption.
Start with a pilot approach – select one low-risk carrier integration and one tenant for the initial hybrid gateway implementation. When you go from legacy EDI to API-first in your fulfillment business, you reduce the process time to onboard new clients by even 75%, improve time-to-revenue, shorten processing time of orders and can achieve 35% average operational cost savin
Phase 1: Establish API Gateway Infrastructure
- Deploy Kong or Envoy with tenant-aware routing
- Implement authentication and rate limiting per tenant
- Set up basic observability and logging
Phase 2: Add Protocol Translation Layer
- Build API-to-EDI transformation services
- Implement tenant-scoped configuration management
- Add dead letter queues and retry mechanisms
Phase 3: Migrate Tenants Gradually
- Run parallel systems during transition
- Validate message integrity across protocols
- Monitor performance and compliance metrics
Partner readiness varies significantly. Some carriers offer both API and EDI endpoints, allowing seamless hybrid approaches. Others remain EDI-only for certain transaction types, requiring your gateway to handle protocol fallback gracefully.
Platforms like MercuryGate, Descartes, and Cargoson provide migration tooling to simplify this transition, but the operational complexity of maintaining both protocol stacks during migration phases requires significant planning and testing.
Success metrics for your migration should include reduced onboarding time (target: 24-48 hours for new tenants), improved API response times (sub-500ms for rate shopping), and maintained EDI compliance rates (>99.5% clean transmission to carriers). Without unified observability, enforcing SLA metrics and scaling AI-enabled workloads becomes reactive and costly.
The multi-tenant hybrid EDI-API gateway represents a pragmatic solution to the dual requirements of modern carrier integration: real-time responsiveness and compliance-grade reliability. The competitive advantage lies in synchronizing both layers instead of choosing one over the other. When implemented with proper tenant isolation, observability, and migration planning, this architecture enables scalable carrier connectivity that adapts to both legacy requirements and modern API expectations.