OAuth 2.1 Multi-Tenant Architecture for Carrier Integration: Surviving the 2026 Migration Crisis Without Breaking Tenant Isolation
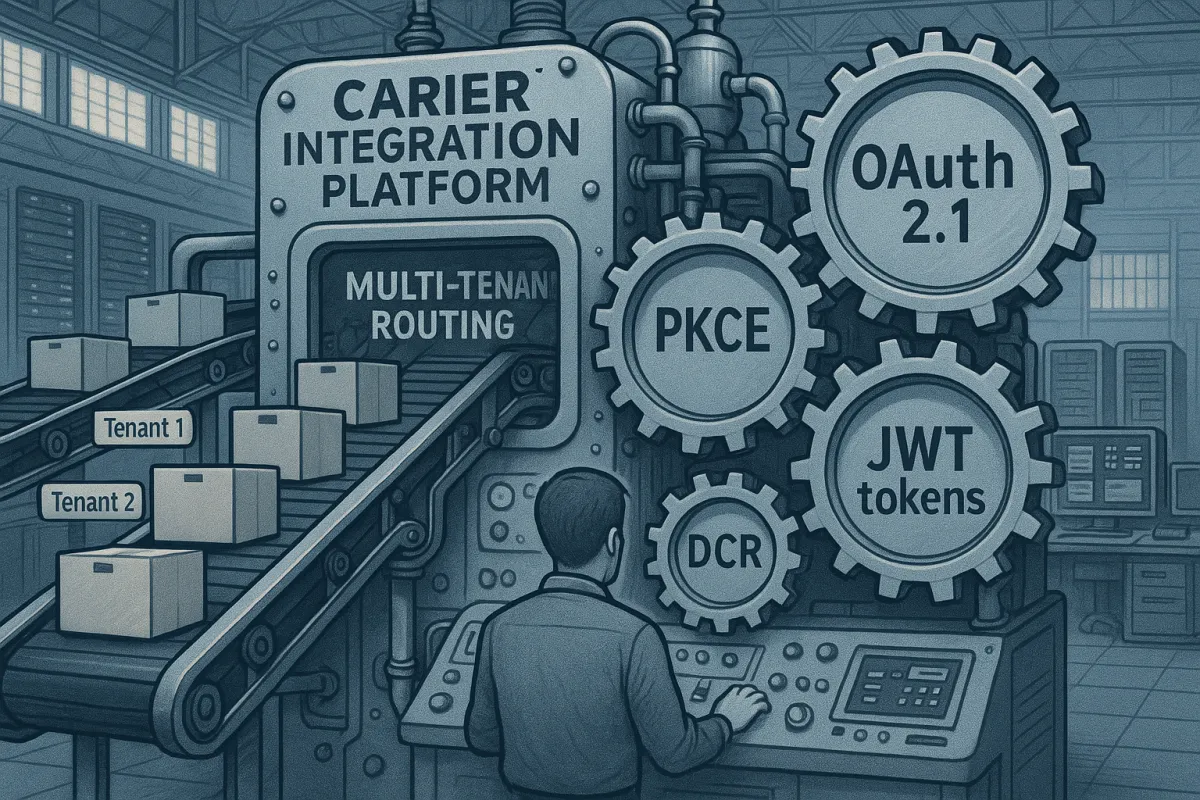
USPS Web Tools retired on January 25, 2026, and FedEx SOAP services will retire on June 1, 2026. These aren't gradual migrations—they're hard stops forcing thousands of enterprise teams into OAuth 2.1 adoption with mandatory PKCE enforcement. UPS completed their OAuth 2.1 migration on January 15, 2025, and by February 3rd, 73% of integration teams reported production authentication failures.
For multi-tenant carrier integration platforms serving hundreds of shippers, this creates a perfect storm. You're not just implementing OAuth 2.1 once—you need tenant-isolated OAuth flows that prevent authentication failures from cascading across your entire platform. Migration failure rates drop by 73% with proper planning, but API uptime fell between Q1 2024 and Q1 2025 as systems faced mounting pressure.
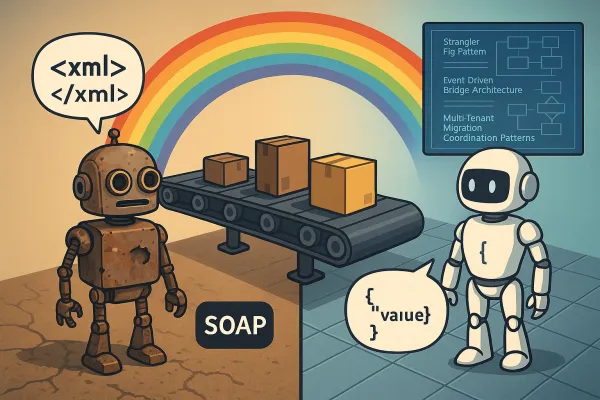
OAuth 2.1 vs OAuth 2.0: Architecture Changes That Matter
OAuth 2.1 mandates PKCE for all authorization code flows, removes implicit and resource owner password credential grants entirely, and enforces stricter redirect URI validation. For multi-tenant carrier integration middleware, these changes fundamentally alter how you handle tenant isolation.
The PKCE requirement means every tenant's OAuth flow now requires dynamic code challenge generation and verification. The USPS v3 API uses OAuth 2.0 client_credentials flow with Bearer tokens in Authorization headers, but tokens expire and must be refreshed. Your architecture must handle this at scale across thousands of tenant contexts without shared state bleeding between tenants.
Here's the critical difference: OAuth 2.0 allowed you to use shared client credentials with tenant context passed as custom parameters. OAuth 2.1's stricter validation rules mean tenant-specific redirect URIs and client registrations become mandatory, not optional.
// OAuth 2.1 tenant-aware authorization flow
POST /oauth/authorize
{
"client_id": "tenant_abc_fedex_client",
"redirect_uri": "https://platform.example.com/oauth/tenant_abc/callback",
"code_challenge": "dBjftJeZ4CVP-mB92K27uhbUJU1p1r_wW1gFWFOEjXk",
"code_challenge_method": "S256",
"state": "tenant_abc_session_xyz"
}
Token Claims for Tenant Routing
OAuth 2.1 tokens in carrier integrations need tenant context embedded as custom claims. When FedEx returns an access token, your middleware must route subsequent API calls to the correct tenant's rate tables, shipping preferences, and billing context.
JWT tokens become your tenant routing mechanism. Include tenant identifiers as custom claims during token issuance, then extract them during validation. This prevents tenant data leakage when processing carrier responses at scale.
{
"iss": "https://api.fedex.com",
"aud": "your_platform",
"sub": "shipper_user_123",
"tenant_id": "enterprise_tenant_abc",
"carrier": "fedex",
"exp": 1648771200,
"scope": "shipping:read shipping:create"
}
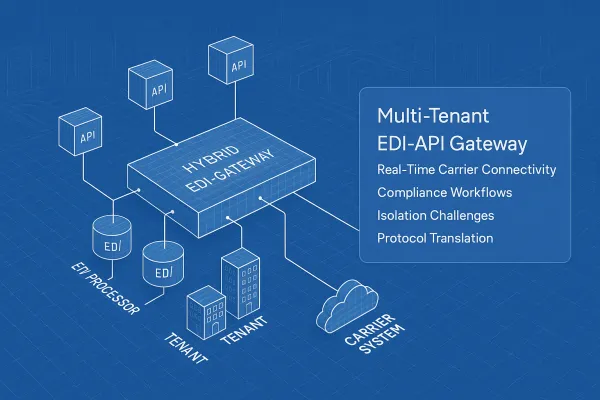
Multi-Tenant Client Registration Patterns
Dynamic client registration becomes essential when managing OAuth flows for multiple carriers across hundreds of tenants. Each tenant needs isolated OAuth credentials to prevent authentication failures from affecting other tenants.
Dynamic Client Registration (DCR) allows OAuth client applications to register with an authorization server at runtime instead of requiring manual configuration. For carrier middleware, this means programmatically creating tenant-specific OAuth clients as new shippers onboard.
Two patterns emerge: shared clients with tenant-scoped tokens, or per-tenant OAuth clients with isolated credentials. Shared clients reduce management overhead but increase blast radius during failures. Per-tenant clients provide stronger isolation but complicate token lifecycle management.
Dynamic client registration involves creating tenant-specific OAuth clients with isolated client credentials, per-tenant redirect URIs and scopes, and programmatic client management. Platforms like Cargoson, EasyPost, and ShipEngine implement per-tenant client patterns to ensure authentication failures remain isolated.
Registration Automation Strategy
Automate OAuth client creation during tenant onboarding. When a new shipper joins your platform, programmatically register OAuth clients for each carrier they'll use. Store client credentials in tenant-scoped secrets management, never shared storage.
// Tenant-specific client registration
{
"client_name": "TenantABC_FedEx_Integration",
"redirect_uris": [
"https://platform.example.com/oauth/tenant_abc/callback"
],
"grant_types": ["authorization_code", "refresh_token"],
"scope": "shipping tracking",
"tenant_metadata": {
"tenant_id": "abc_corp",
"carrier": "fedex",
"environment": "production"
}
}
Production Authentication Failure Patterns
Token refresh logic starts failing when you hit 50+ requests per second under the new carrier API rate limits. USPS's new API rate limit is set at 60 requests per hour, while old Web Tools integrations processed 300 address validations during peak shipping hours. The math doesn't work.
OAuth token management becomes your bottleneck. Production environments generate thousands of concurrent calls, each potentially requiring fresh tokens. Without proper token pooling and refresh strategies, you'll hit rate limits before processing meaningful shipping volume.
Legacy SOAP error codes don't map cleanly to REST responses, causing retry logic to assume failures are temporary when they're actually permanent, resulting in infinite retry loops. Your circuit breaker logic must understand OAuth 2.1 error responses to prevent cascading failures.
Circuit Breaker Patterns for Multi-Tenant OAuth
Implement tenant-aware circuit breakers that isolate OAuth failures. When one tenant's FedEx integration starts failing authentication, other tenants should continue processing shipments normally. Traditional circuit breakers trip globally—you need tenant-scoped failure detection.
Monitor OAuth success rates per tenant and carrier combination. Set different thresholds for authentication failures versus API rate limiting. A tenant hitting USPS rate limits shouldn't trigger circuit breaker logic for UPS integrations.
// Tenant-isolated circuit breaker state
{
"tenant_abc": {
"fedex": {
"oauth_failures": 3,
"last_failure": "2026-03-25T10:30:00Z",
"circuit_state": "half_open",
"next_retry": "2026-03-25T10:35:00Z"
},
"ups": {
"oauth_failures": 0,
"circuit_state": "closed"
}
}
}
Token Lifecycle Management at Scale
OAuth 2.1 mandates token rotation and sender-constrained refresh tokens to prevent replay attacks. For multi-tenant platforms processing thousands of shipments daily, token lifecycle management becomes a distributed systems problem.
Store refresh tokens with tenant isolation. Use encrypted storage with tenant-specific encryption keys. Never store tokens in shared databases where tenant data could leak through SQL injection or access control failures.
Implement proactive token refresh 5-10 minutes before expiry. Don't wait for 401 responses during peak shipping hours—refresh tokens during low-traffic periods to avoid authentication delays when processing time-sensitive shipments.
Token rotation schedules must account for carrier-specific requirements. FedEx tokens expire after different intervals than UPS tokens. Your token refresh logic needs carrier-aware scheduling to prevent authentication failures during high-volume shipping windows.
Observability Without Breaking Tenant Isolation
Monitor OAuth authentication success rates per tenant without exposing sensitive tenant data in logs. Aggregate metrics by tenant ID hash, not plaintext tenant identifiers. Track authentication latency, token refresh frequency, and failure patterns across carrier APIs.
Alert on authentication failure spikes that could indicate credential compromise or API changes. When FedEx changes their OAuth implementation—and they will—you need early warning before customer shipments start failing.
Platforms implementing these patterns correctly, including Cargoson alongside competitors like nShift and Transporeon, maintain 99.9%+ authentication success rates even during carrier API migrations. The key is treating OAuth 2.1 as infrastructure, not an implementation detail.
Design your OAuth 2.1 multi-tenant architecture now, before the next carrier migration deadline forces another emergency rebuild. The 2026 crisis won't be the last—it's just the beginning of carriers modernizing their authentication systems.