Semantic Versioning for Carrier Integration APIs: Managing Breaking Changes in Multi-Tenant Middleware

UPS replaced its entire existing API infrastructure, deprecating access key-based authorization in favor of OAuth 2.0 security models, with post-June 3, 2024, any transaction with UPS mandating this new OAuth security model. Major carriers are actively migrating away from SOAP-based APIs, with FedEx retiring their legacy Web Services in May 2024 and moving to RESTful APIs, while UPS transitioned from XML protocols to OAuth 2.0-secured REST endpoints. Carrier APIs change without warning. You know this if you've ever woken up to broken rate requests or mysteriously failed label generation.
These are not isolated incidents. Across the carrier integration landscape, API changes arrive without proper versioning signals, breaking production systems for thousands of shippers. The problem runs deeper than inconsistent carrier behaviour. Your multi-tenant carrier middleware needs a semantic versioning strategy that acknowledges this reality while protecting your tenants from unnecessary disruption.
The Versioning Crisis in Carrier Integration
Standard API versioning fails spectacularly in carrier integration environments. When a shipping carrier changes fields on their API, they have to be updated on your side. Carrier maintenance is a big thing, you could need multiple developer resources working full time just to manage it. Unlike typical SaaS APIs where providers follow disciplined release cycles, carriers often push changes with minimal notice or version signalling.
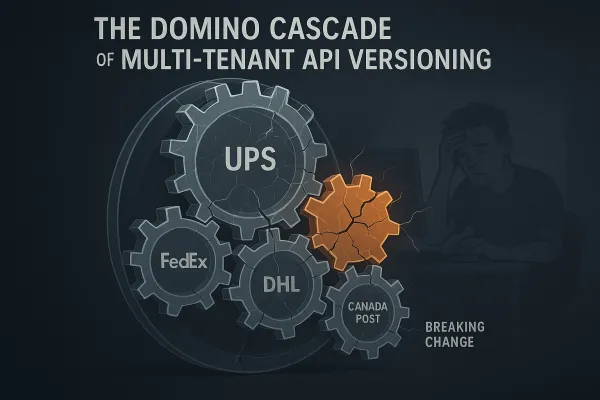
Consider the cascading failure patterns. When FedEx modifies their rate response schema to include new surcharge fields, existing parsers break. DHL changes their authentication flow, invalidating stored credentials. USPS updates their address validation requirements, causing silent label generation failures. Each incident affects multiple tenants simultaneously unless you have proper version isolation.
The complexity multiplies in multi-tenant environments. A single tenant's integration breaking can cascade to affect routing decisions for others. Worse, different tenants may depend on different carrier API versions, requiring your middleware to maintain compatibility across multiple generations of the same carrier's interface.
This reality demands versioning patterns that go beyond simple MAJOR.MINOR.PATCH numbering. Your semantic versioning strategy must handle carrier-induced breaking changes, tenant-specific version requirements, and gradual migration paths without service disruption.
Semantic Versioning Fundamentals for Transport APIs
A normal version number MUST take the form X.Y.Z where X, Y, and Z are non-negative integers, and MUST NOT contain leading zeroes. X is the major version, Y is the minor version, and Z is the patch version. For carrier integration middleware, this translates into a specialized interpretation framework.
PATCH versions (1.2.1) handle carrier-side fixes that don't change API contracts. A DHL tracking endpoint returning more consistent timestamps qualifies as a patch. So does correcting UPS rate calculations for rural zones. These changes fix behaviour without altering expected request/response structures.
MINOR versions (1.3.0) introduce backward-compatible additions. New optional fields in rate responses, additional service levels from carriers, or enhanced address validation capabilities fall here. Existing integrations continue working without modification while new functionality becomes available for those who want it.
MAJOR versions (2.0.0) signal breaking changes that require consumer updates. Removing deprecated rate calculation methods, changing authentication flows, or restructuring core data models necessitate major version bumps. Per the semantic versioning specification, breaking changes (i.e., incompatible changes) will only be released with a major version bump.
The key insight for transport APIs: version negotiation must happen at the tenant level, not globally. Your middleware needs to support different API versions for different tenants simultaneously, allowing gradual migration without forcing wholesale upgrades.
Multi-Tenant Versioning Architecture Patterns
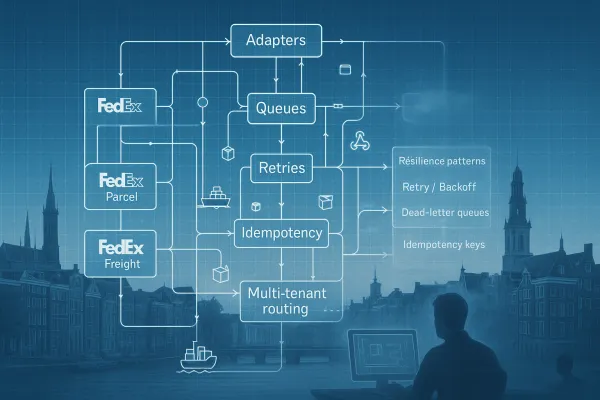
Multi-tenant carrier middleware requires version routing strategies that isolate tenant-specific API versions while maintaining shared infrastructure efficiency. The architecture must support hierarchical versioning where tenant preferences override global defaults without creating operational overhead.
Implement version-aware routing at the adapter layer. Each carrier adapter maintains version-specific transformation logic, allowing different tenants to use different API contract versions simultaneously. A tenant running on your v1.5.0 API can coexist with another using v2.1.0, both hitting the same carrier through appropriately versioned adapters.
Data segregation becomes critical. Version-specific request/response schemas must be isolated to prevent cross-contamination. Use separate message queues for different API versions, ensuring that a tenant's v1.x messages don't interfere with another tenant's v2.x processing. This isolation extends to dead letter queues, retry mechanisms, and error handling patterns.
Tenant version assignment should support both explicit configuration and intelligent defaults. Allow tenants to pin specific versions for stability while providing automatic patch-level updates. For example, a tenant specifying version 1.3 automatically receives 1.3.1 and 1.3.2 updates but stays on 1.3.x until explicitly migrated to 1.4.0 or 2.0.0.
Version compatibility matrices become essential operational tools. Maintain clear mappings of which tenant versions are compatible with which carrier API versions, enabling proactive migration planning when carriers announce deprecations or breaking changes.
Backward Compatibility Strategies for Shipping APIs
Maintaining backward compatibility in shipping APIs requires transformation layers that bridge version differences without degrading performance. The strategy focuses on field aliasing, graceful degradation, and default value injection.
Field aliasing handles the most common breaking change pattern: field renames. When UPS changes DeliveryDate to EstimatedDeliveryDate, your compatibility layer maps the old field name to the new response structure. Tenants using older API versions continue receiving DeliveryDate while new integrations get the updated field name.
Graceful degradation manages functionality removal. When carriers deprecate specific service levels, provide fallback mappings to equivalent services rather than failing outright. A deprecated "Next Day Saver" service maps to standard "Next Day" with appropriate cost adjustments and clear deprecation warnings in response metadata.
Default value injection addresses new required fields in older API versions. When FedEx introduces mandatory packaging type specifications, older API versions receive sensible defaults based on shipment characteristics while logging deprecation notices for future tenant review.
Version-specific transformers sit between your core business logic and carrier adapters. These components handle the translation complexity, allowing your main application code to work with stable internal data models while presenting version-appropriate interfaces to tenants.
The transformation approach scales better than maintaining separate codebases per version. You write business logic once and let transformers handle version-specific presentation, reducing maintenance overhead while ensuring compatibility.
Breaking Change Management and Migration Patterns
Update and notify users about major changes at least 30 days in advance. To phase out older versions, provide migration guides, update version-specific documentation, and set clear sunset dates. In carrier integration environments, this timeline often needs extension due to the complexity of multi-carrier integration testing.
Implement a three-phase deprecation policy. Phase one introduces breaking changes in new major versions while maintaining full backward compatibility for existing versions. Phase two marks older versions as deprecated with clear migration paths and extended support timelines. Phase three removes deprecated versions after sufficient notice and migration assistance.
Migration tooling becomes critical for complex carrier integrations. Build automated compatibility testing frameworks that validate tenant integrations against new API versions before requiring migration. Provide migration scripts that update configuration formats, test data, and integration code patterns.
The challenge with carrier APIs is that your breaking changes often cascade from carrier-imposed changes. When DHL announces OAuth migration with a six-month timeline, your middleware may need to introduce breaking changes to accommodate the new authentication patterns. Your migration timeline must account for both carrier deadlines and tenant integration complexity.
The eBay RESTful API uses three-number semantic versioning and combines this with Aggressive Obsolescence: a new major version remains compatible with an old one, but can deprecate functionality which in the future will be removed. This allows for an easier migration from the point of view of a client although the full version number is visible. However, eBay expects the clients to then migrate within the next six months to the new major version and remove the dependency on deprecated functionality.
Communication strategies must account for the technical complexity of carrier integrations. Provide detailed impact assessments showing exactly which carriers, services, and functionality will be affected by version changes. Include specific test cases and migration validation steps rather than generic upgrade instructions.
Production Deployment and Monitoring Considerations
Version deployment in carrier integration middleware requires careful orchestration to prevent service disruption across multi-tenant environments. Unlike single-tenant applications where version updates affect one user base, carrier middleware changes can impact hundreds of tenants simultaneously.
Blue-green deployment strategies work well for major version releases but require tenant-aware routing. Deploy new versions alongside existing ones, then migrate tenants progressively based on their version compatibility and business requirements. This approach allows rollback for individual tenants without affecting others.
Feature flags provide fine-grained control over version-specific functionality. Enable new carrier adapters or enhanced rate calculation logic for specific tenants while maintaining existing behaviour for others. This granular control proves essential when testing carrier changes that might affect only subset of your tenant base.
Version-specific monitoring becomes critical. Track error rates, response times, and carrier success rates segmented by API version. A spike in failures for tenants using v1.x might indicate carrier compatibility issues that don't affect v2.x users, enabling targeted investigation and remediation.
Rollback procedures must account for data compatibility between versions. Ensure that transactions initiated in v2.x can be safely processed by v1.x systems if rollback becomes necessary. This typically requires maintaining compatible data structures across version boundaries for critical transaction data.
Industry Implementation Examples and Lessons
Leading carrier integration platforms demonstrate varied approaches to semantic versioning challenges. A de facto universal carrier API standard and multi-carrier platform in one. If you're looking for a better way to manage your carrier integrations, Cargoson can help. Our platform provides a single, standardized transport API that connects you to all your carriers, regardless of their individual capabilities. This approach abstracts versioning complexity behind unified interfaces.
Other platforms like nShift, ShipEngine, and EasyPost handle versioning through different strategies. Some maintain strict backward compatibility with extensive transformation layers. Others prefer more aggressive deprecation cycles that force regular updates but reduce technical debt accumulation.
GrandViewResearch reports that the global API logistics market is projected to grow at a 20.2% CAGR from 2024 to 2030. This growth shows the expansion of e-commerce and the increasing demand for real-time tracking and visibility. This growth intensifies the need for robust versioning strategies as more businesses depend on carrier integration reliability.
The most successful implementations balance stability with innovation. They provide clear migration paths while avoiding the temptation to break compatibility for minor improvements. The costs of breaking changes in multi-tenant environments often outweigh the benefits of cleaner API designs.
Key lessons from production deployments: version testing must include carrier sandbox environments, migration timelines should account for tenant testing cycles, and rollback capabilities are non-negotiable for revenue-critical shipping operations. The key takeaways from this discussion highlight the importance of a nuanced understanding of versioning and the impact of breaking changes. Firstly, any inconsistency in handling major version updates and breaking changes across SaaS APIs can create significant disruptions. API publishers often focus narrowly on API compatibility, overlooking broader implications. The integration of multiple SaaS APIs in modern applications necessitates a broader view, encompassing various aspects of API functionality and behavior.
Your semantic versioning strategy for carrier integration APIs needs to acknowledge the messy reality of carrier behaviour while providing stability for your tenants. Focus on tenant-level version isolation, comprehensive backward compatibility, and gradual migration paths. The goal is reliable shipping operations, not elegant API design.