Zero-Downtime Traffic Routing Patterns for the 2026 Carrier API Migration Wave: Multi-Tenant Architectures That Survive SOAP-to-REST Transitions Without Breaking Shipment Processing

The USPS Web Tools API platform shut down on January 25, 2026, and FedEx SOAP endpoints will retire on June 1, 2026. This isn't just another platform upgrade. The Web Tools API platform shutdown marks the beginning of a massive wave of carrier API retirements hitting enterprise integration teams. USPS's new API rate limit is set at 60 requests per hour, while your old Web Tools integration processed 300 address validations during peak shipping hours.
Traditional "big bang" migration approaches break down under these constraints. When you're managing thousands of shipment labels per hour across multiple tenants, you can't afford the luxury of maintenance windows or synchronized deployments. You need intelligent traffic routing patterns that maintain service continuity while your systems transition between fundamentally different authentication models and rate limiting schemes.
Traffic Routing Architecture Fundamentals
Zero-downtime migration requires careful planning and patterns that support continuous operation. Incompatible changes to the data structure can be deployed without any downtime of the system when you use the right architectural foundations. The core principle is gradual transition over complete overhauls, maintaining backward compatibility while new systems prove themselves under production load.
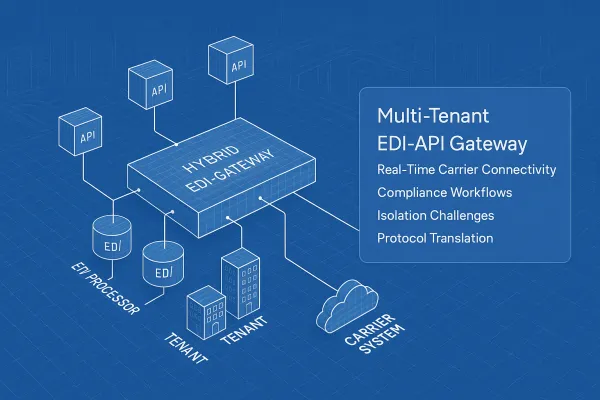
Multi-tenant routing boundaries become critical during migrations. Workspaces provide an isolation of gateway configuration objects while maintaining a unified routing table on the data plane to support client traffic. Each tenant's traffic flows through the same infrastructure, but routing decisions preserve strict data segregation. Your tenant A's USPS address validations never mix with tenant B's FedEx rate shopping requests, even when both are transitioning between old and new APIs simultaneously.
Platforms like Cargoson, nShift, EasyPost, and ShipEngine have built these routing abstractions into their core architectures. They handle the complexity of maintaining separate authentication sessions for legacy SOAP endpoints and new OAuth flows, often for the same logical carrier operation.
Expand-and-Contract Pattern for Carrier Migrations
Every migration follows the expand-contract pattern, introducing changes gradually while ensuring system remains operational. This pattern originally emerged for database migrations, but it applies perfectly to API transitions. The expand phase adds new schema elements alongside the existing ones, then once all dependencies are updated, the contract phase removes the old elements.
For SOAP-to-REST transitions, the expand phase means running both authentication systems in parallel. Your application maintains existing USERID-based Web Tools connections while simultaneously establishing OAuth client credentials for the v3 APIs. Database-level dual writes ensure triggers handle writing to both old and new fields, keeping this logic out of your application code. In carrier integration terms, this means every rate request triggers both a legacy SOAP call and a new REST call, with the system comparing results to identify discrepancies before the June deadline.
Circuit breaker patterns become essential during expansion. When new APIs hit rate limits or authentication failures spike, you immediately route traffic back to legacy endpoints. The beauty of expand-and-contract is that every single step can be rolled back once it has been deployed.
Intelligent Traffic Splitting and Canary Routing
Feature flag-driven shadow requests let you generate production-load API calls without affecting customer shipments. You dial up the percentage gradually, from 1% of rate shopping requests to 25%, then 75%, all while your primary business logic continues using the proven legacy endpoints.
Header-based routing gives you fine-grained control over API version selection. Custom Lambda authorizer functions in API Gateway can verify tokens, extract tenant IDs, and return routing decisions. A tenant marked as "USPS_V3_READY" gets routed exclusively to the new endpoints, while others remain on Web Tools until their validation completes.
Circuit breakers prevent cascading failures across your multi-tenant architecture. When FedEx REST APIs return 429 rate limit errors, the circuit opens and routes those specific requests back to legacy SOAP endpoints. This happens per-tenant, per-carrier, per-operation. Tenant A's FedEx rate shopping might be running on REST APIs while their label generation still uses SOAP, and tenant B might be fully migrated to REST for all operations.
Platforms like EasyPost, Cargoson, ShipEngine, and project44 implement weighted traffic distribution algorithms that account for both API reliability and tenant preferences. Some enterprise customers require slower migration schedules due to their own integration testing cycles.
Authentication and Rate Limiting Coordination
OAuth 2.0 token management becomes complex at scale. USPS's new API rate limit is set at 60 requests per hour. Your old Web Tools integration processed 300 address validations during peak shipping hours. You do the math. Production systems generating thousands of concurrent API calls need token refresh logic that doesn't fail when you hit 50+ requests per second against the OAuth endpoint itself.
Multi-tenant token isolation requires separate credential stores per tenant. Each tenant needs their own OAuth client credentials, their own token refresh cycles, and their own rate limiting quotas. To enforce usage plans for each tenant separately, use tenant ID as a prefix to a uniquely generated value to prepare the custom API key.
Distributed rate limiting coordination becomes critical when you have multiple application instances serving the same tenant. If tenant A has a 60 requests/hour USPS quota, you need shared state to track consumption across all your API gateway instances. Redis-backed counters with sliding window algorithms work well here, but they add latency to every carrier API call.
The reality check is brutal. Multi-carrier shipping platforms like Cargoson, MercuryGate, and BluJay built abstraction layers that handle the OAuth complexity, implement intelligent rate limiting queues, and provide fallback mechanisms when USPS quotas are exceeded. Building this yourself means recreating years of production-hardened error handling.
Production Monitoring and Rollback Strategies
Real-time monitoring must track both your application metrics and the carrier APIs themselves. API uptime declined between Q1 2024 and Q1 2025 as systems faced mounting pressure from complexity increases and legacy system strain. You need synthetic monitors hitting USPS, FedEx, and UPS endpoints independently of your business logic.
Performance baselines shift during migrations. Your old Web Tools integration processed 300 address validations during peak shipping hours, with 200ms average response times. The new USPS v3 APIs might deliver 150ms responses but with completely different consistency characteristics under load. Your SLO definitions need to account for this reset.
Automated rollback triggers prevent 3 AM emergency fixes. When error rates spike above 5% for any tenant-carrier combination, the system automatically reverts those specific routes to legacy endpoints. Your rollback doesn't need to be all-or-nothing. Tenant A's USPS traffic can roll back while their FedEx integration continues on the new APIs.
Circuit breaker thresholds need careful tuning during migrations. Too sensitive, and you never give new APIs a chance to prove stability. Too loose, and you compound authentication failures into customer-facing shipment delays.
Multi-Tenant Isolation During Migration
Tenant routing boundary preservation requires careful coordination during API transitions. Kong Gateway attempts to ensure that routing rules don't contain conflicts before applying them to the data plane, but two separate tenants may desire to have an API route path matching /users. In carrier integration terms, this means tenant-specific OAuth credentials, rate limits, and error handling policies.
Performance isolation becomes critical when some tenants migrate faster than others. API Gateway allows you to throttle per-tenant requests to minimize the impact of noisy neighbors and optimize performance. If tenant A's migration to USPS v3 APIs starts hitting rate limits, it shouldn't affect tenant B's stable Web Tools traffic.
Data segregation maintenance across old and new endpoints requires careful tenant context propagation. Every API request needs to carry tenant identification through your routing pipeline, whether it's heading to legacy XML endpoints or new JSON APIs. Header-based tenant identification works well here: pass the tenant-id as part of your own custom Http headers like X-TENANT-ID.
The testing complexity multiplies. You need validation environments for every tenant-carrier-API version combination. Tenant A might be testing FedEx REST while still on USPS Web Tools. Tenant B could be migrated to both new APIs. Tenant C remains fully on legacy systems. Your test matrix explodes.
Platforms like Cargoson, Descartes, and BluJay handle this complexity through abstraction layers that present unified interfaces regardless of the underlying carrier API versions. They handle carrier API changes, manage authentication complexity, and provide unified interfaces that survive individual carrier migrations.
The companies that survive 2026's migration wave won't be those with perfect technical execution. They'll be the ones who recognized that carrier integrations are infrastructure, not features, and invested accordingly. Your choice: spend months debugging OAuth flows and rate limiting edge cases, or focus on shipping software that differentiates your business while someone else handles the carrier API complexity.