Continuous Deployment Architecture for API Migration Crises: Patterns That Survived the 2026 Carrier Wave Without Breaking Shipment Processing
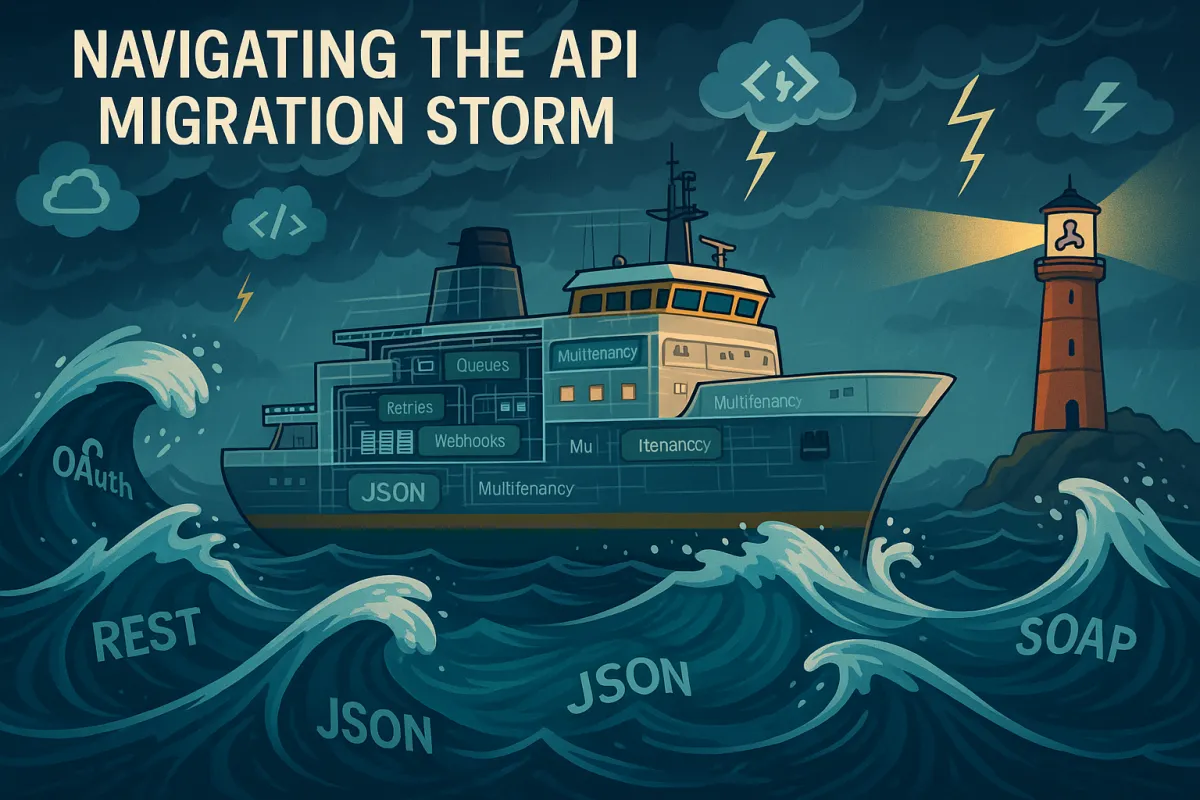
USPS Web Tools shut down on January 25, 2026, and FedEx SOAP endpoints retire on June 1, 2026. For thousands of companies still running legacy integrations, this wasn't just a technical upgrade. It's a forced march through production deployment hell. While some teams managed to adapt their continuous deployment architecture to survive these transitions, 73% of integration teams reported production authentication failures after similar UPS OAuth migrations. Those failures weren't random. They exposed fundamental flaws in how most teams architect their deployment pipelines for API-dependent systems.
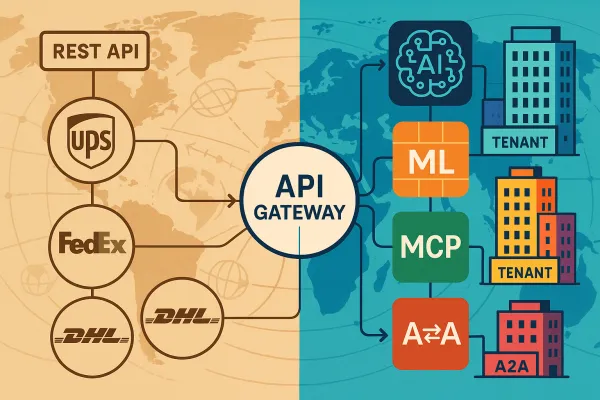
Multi-carrier platforms like Cargoson, nShift, and ShipEngine had already built abstraction layers that survived these migrations. They built abstraction layers that handle the OAuth complexity, implement intelligent rate limiting queues, and provide fallback mechanisms when USPS quotas are exceeded. The difference wasn't just better vendor relationships. These platforms architected their continuous deployment pipelines to treat external API changes as normal operational risk, not exceptional disasters.
The API Migration Crisis That Changed Everything
USPS's new APIs enforce strict rate limits of approximately 60 requests per hour, down from roughly 6,000 requests per minute without throttling in the legacy system. The scale of this problem is staggering. While data migration failure rates drop by 73% with proper planning, most teams are discovering these deadlines months too late.
The WSDL retirement means every integration touching FedEx services requires a complete rebuild. Your existing SOAP calls don't map one-to-one to REST endpoints. Rate shopping, label generation, and tracking require new endpoint structures, different request formatting, and updated response parsing. The JSON payloads use different field names, nesting structures, and data types than your SOAP XML.
Traditional deployment patterns failed because they assumed external dependencies would remain stable during release windows. When both carriers are moving to a RESTful API using OAuth 2.0 instead of single access key authentication, your deployment pipeline suddenly needs to coordinate token refresh, scope validation, and rate limiting across multiple carrier APIs simultaneously.
Continuous Deployment Anti-Patterns That Amplify Migration Risk
Most deployment pipelines couple their success criteria directly to external API responses. When USPS switched off their Web Tools APIs, these pipelines immediately started failing their health checks because they couldn't distinguish between deployment issues and external API changes.
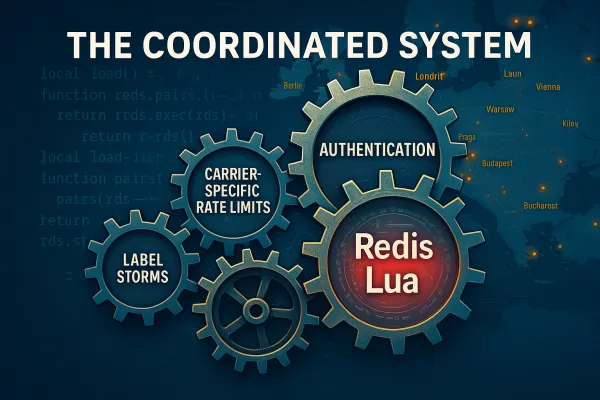
The authentication pipeline problem hit hardest. UPS migrated to OAuth 2.0 in August 2025. By February 3rd, 73% of integration teams reported production authentication failures. These weren't gradual degradations. Teams discovered their CI/CD pipelines had been generating and caching authentication tokens during builds, but the token refresh logic failed under concurrent deployment loads.
UPS's OAuth implementation can become inconsistent during DynamoDB issues, returning 500 errors while maintaining partial session state. UPS's API returns 500 errors during DynamoDB DNS issues but maintains session state inconsistently. Your retry logic generates new tokens, but the carrier's backend still has references to the old sessions.
The Authentication Pipeline Problem
Standard deployment gates test application functionality, not external API contract compliance. When USPS recently modified address validation scopes to require additional permissions. Teams discovered this only when their production requests started returning authorization errors despite valid tokens.
Circuit breaker patterns work for deployment flows, but they need carrier-specific tuning. UPS APIs typically respond within 200-400ms for authentication requests. DHL SOAP endpoints take 800-1200ms. When these baselines shift, it indicates infrastructure changes that affect your authentication flows before they cause outright failures.
Multi-Version API Deployment Architecture
The teams that survived the 2026 wave built deployment architectures that could run multiple API versions simultaneously during migration windows. This requires more than just feature flags. You need deployment pipelines that understand API contract evolution.
API traffic needs to be intelligently routed based on various factors like version, client identity, or feature flags. The deployment controller in Kubernetes works in conjunction with Services, Ingress controllers, or service meshes to manage this traffic routing. This enables sophisticated deployment patterns like canary releases or blue-green deployments.
Blue-green deployments become more complex when external APIs change their contracts during your deployment window. Blue-Green deployments: Maintain two production environments (blue and green) and switch traffic atomically. This enables instant rollback but doubles infrastructure costs. With carrier API migrations, you need blue-green environments that can each talk to different API versions.
The Adapter Pattern for Pipeline Resilience
Abstracting external API calls from core deployment logic means your pipeline success criteria can focus on application health rather than external dependency availability. Graceful degradation ensures applications continue functioning when API changes occur unexpectedly.
Version-aware API client generation in CI/CD pipelines works by building adapters for both legacy and modern API versions during the same build. Parallel Run Strategy: Never switch entirely at once. Build adapter layers that can route requests to either legacy or modern APIs based on configuration flags. This lets you test production traffic loads against new endpoints while maintaining fallback capability.
Netflix, a leader in microservices architecture, transitioned its API endpoints through a combination of canary releases and A/B testing. Leveraging its cloud-native environment, Netflix was able to deploy new API versions to a small section of its user base, closely monitor performance, and gradually roll out updates to ensure stability. Their microservice architecture supports rapid iteration while minimizing disruptions.
Deployment Gates That Actually Catch API Breaking Changes
Contract testing integration in CI/CD pipelines requires testing against real carrier sandbox environments, not just mocked responses. Comprehensive testing includes multiple layers. Unit tests validate individual functions calling APIs using mocked responses. Integration tests verify end-to-end workflows with real API calls in test environments. Contract tests ensure application expectations match API provider specifications. Regression tests validate existing functionality continues working.
Synthetic transaction monitoring during canary deployments catches API behavior changes that don't trigger obvious errors. Synthetic transaction monitoring simulates real user journeys to verify end-to-end functionality. Adopting end-to-end API testing, with tools like Postman's monitoring tools, allows you to run these checks continuously, alerting you when behavior changes unexpectedly.
SLO-based rollback triggers for API performance degradation work by establishing carrier-specific baselines. Establish quantitative thresholds in advance—error rates above 0.5%, latency increases beyond 100ms, or failed transactions exceeding 0.1% might all trigger automatic investigation.
Platforms like Cargoson, EasyPost, and ShipEngine implement these patterns by maintaining dedicated carrier relationship teams. Multi-carrier platforms handle this complexity through managed authentication services. ShipEngine, Cargoson, and nShift maintain carrier relationship teams that receive advance notice of authentication changes.
Rate Limiting Awareness in Deployment Flows
Queue-based deployment strategies for rate-limited APIs prevent your CI/CD pipeline from overwhelming carrier endpoints during deployment testing. USPS rate limiting creates immediate bottlenecks. The new APIs enforce 60 requests per hour for address validation. Enterprise shippers processing thousands of addresses during order imports face immediate bottlenecks. Most teams discover this limit only when their batch processes start failing in production.
Deployment timing coordination across multiple services means scheduling your carrier API testing during off-peak hours to avoid hitting rate limits that block legitimate business operations.
Backpressure handling in CI/CD pipelines requires implementing circuit breakers that can distinguish between deployment failures and external API quotas being exceeded.
Post-Migration Operational Patterns
Monitoring and alerting for API behavior changes needs to capture carrier-specific metrics. Authentication-specific metrics matter more than generic uptime checks. Track token refresh frequency, scope validation success rates, and permission error patterns.
Performance baseline reset strategies become critical after carrier migrations. Define success criteria that must be met before advancing stages. Error rate increases should remain under 0.1%, response time degradation should stay within 10% of baseline, and user-reported issues should remain minimal.
New error pattern detection requires understanding that carriers often change their error response formats during API migrations. Authentication failures are particularly dangerous because they often go unnoticed. An expired token or misconfigured permission can block users while unauthenticated checks continue to pass.
Building for the Next Migration Crisis
Proactive API sunset detection means monitoring carrier developer portals and changelogs for deprecation announcements. Many developers ignore deprecation warnings until forced to update. This creates emergencies when deprecated features actually shut down.
Vendor diversification strategies in architecture reduce single points of failure. Staged rollouts migrate to new API versions gradually, reducing risk of widespread failures. Staged rollouts migrate to new API versions gradually rather than all at once, reducing risk of widespread failures. A phased migration plan ensures a smooth transition and reduces the risk of unexpected disruptions.
Platform abstraction layers from vendors like Cargoson, ShipEngine, and MercuryGate provide isolation from future carrier API changes, but they come with their own operational overhead and vendor lock-in risks.
The continuous deployment architecture patterns that survived the 2026 carrier wave share common characteristics: they treat external API changes as normal operational risk, they build for graceful degradation rather than perfect reliability, and they prioritize rollback speed over deployment frequency. Organizations using staged rollouts report 70% fewer incidents. The architecture changes required aren't just technical. They require accepting that external dependencies will break your deployment contracts, and building systems that can handle that reality without stopping your ability to ship code.